From the Field
Operators Already Running on SENTINEL
Private EP firms, family offices, and corporate security teams using the platform in active protection programs today.
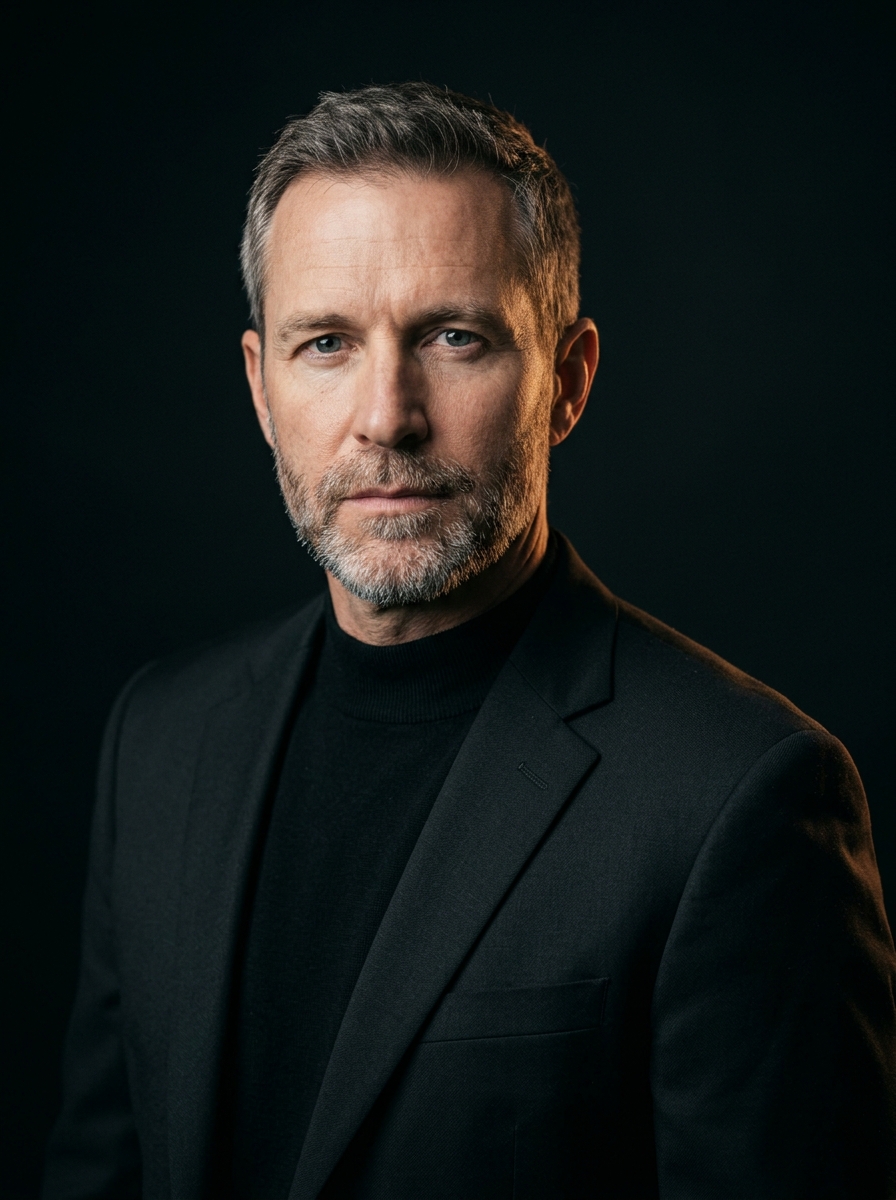


Marcus Halloran
Director of Operations · Private EP Firm
We were turning down two principals a quarter because we didn't have advance bandwidth. SENTINEL changed the math overnight — our two senior agents now cover six principals each instead of three, with deeper intel than we used to deliver.